Multi Factor Authentication Setup
Prerequisites
- You have downloaded, installed and configured the Oplon Secure Access Virtual Appliance as indicated in this guide.
- Make sure that the appliance has outgoing port
2443open, it will need to communicate with super.oplon.cloud for MFA to work correctly.
If, in step 2, you wish to configure a specific outbound firewall rule from the Oplon appliance to super.oplon.cloud on port 2443, ensure that the firewall supports port rules based on FQDN (Fully Qualified Domain Name).
This is important because Oplon’s cloud services are distributed across multiple data centers to ensure high availability.
If the firewall only supports rules based on IP addresses, you will need to allow outbound traffic on port 2443 to any destination IP.
Import Certificate .P12 super.oplon.cloud
Once you have purchased the Multi Factor Authentication service from Oplon, you will be given a .P12 certificate, which will be the certificate with which the appliance will interface with super.oplon.cloud for verifying the trustworthiness of the connection to allow the authorizations of the Multifactor Authentication Users.
At this point we can import the Keystore into Our Virtual Appliance.
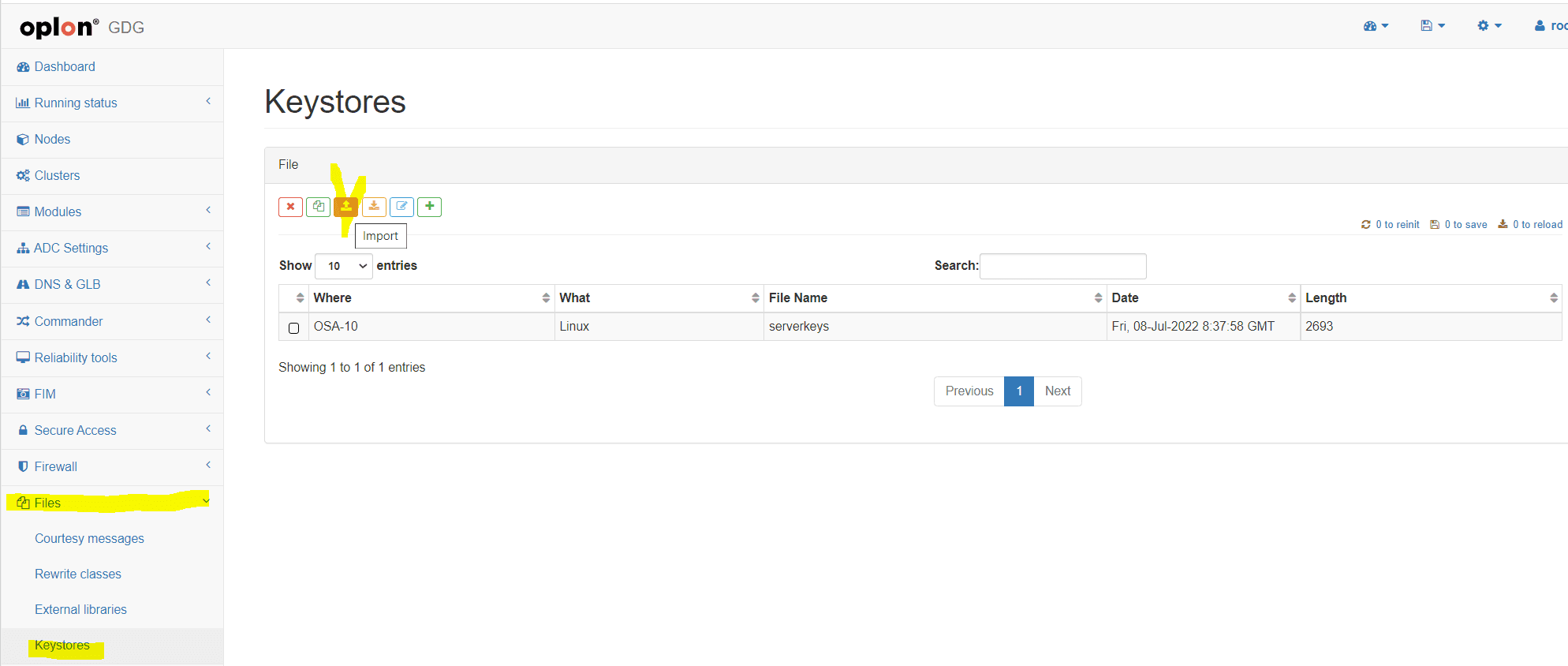
we select the file from the local path where we placed it and decide to Insert it on Our Platform
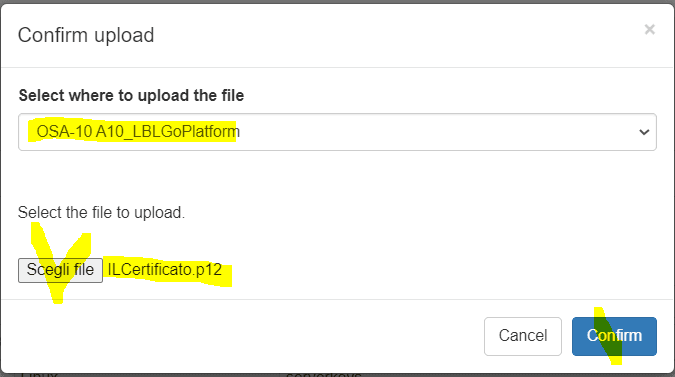
A video of the operation of inserting the Keystore into our Platform A10_LBLGoPlatform
Copying and Configuring MFA/2FA Rewrite Rules
- Rewrite Header Rules Research
We flag the Templates view and search in search for the string
2fa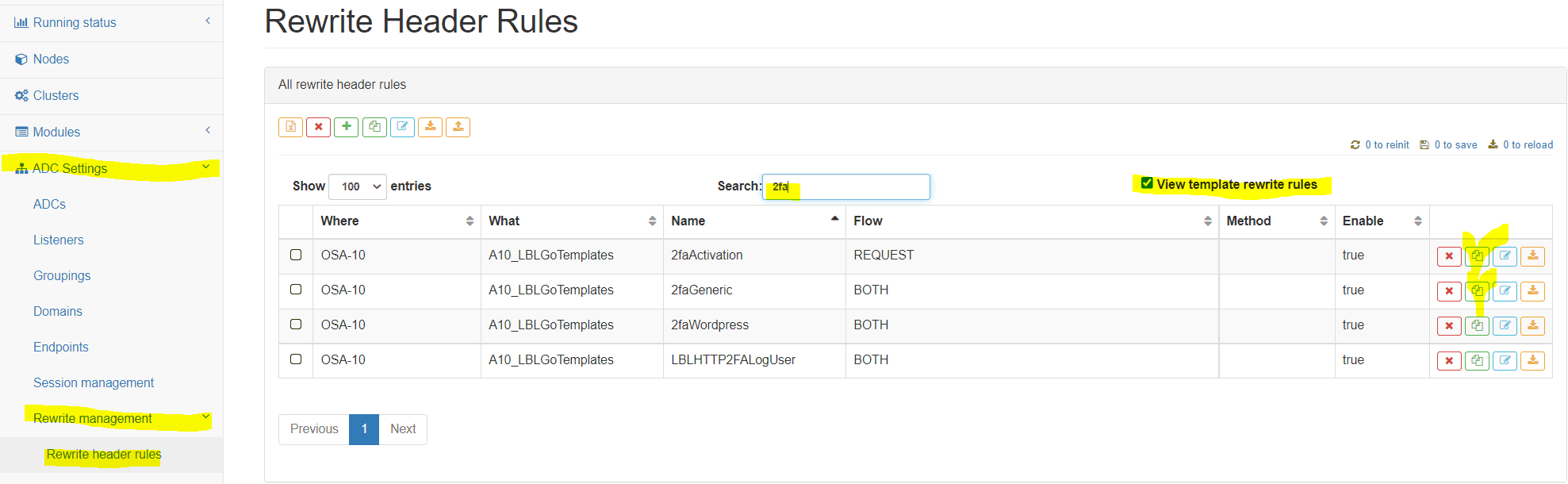
- Rewrite Header Rules Copy
we copy Templates in our
A10_LBLGoPlatformPlatform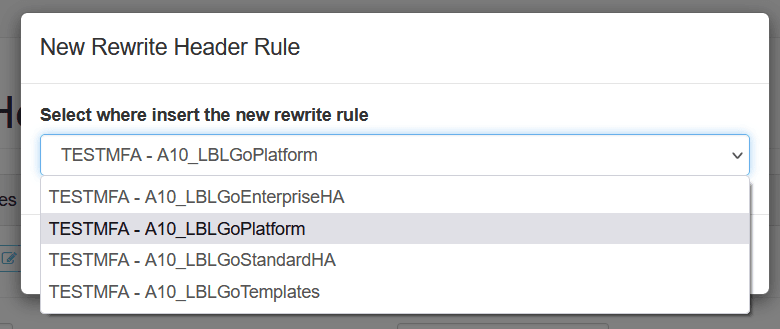
A video of the operation of copying the Rewrite Header Rules secure Templates into our Platform A10_LBLGoPlatform.
Now we can proceed with the configuration of the Rewrite Rules that will protect the Oplon Secure Access resources.
Configuration Rewrite Header 2faActivation and ACTIVATION_CODE
We go to the Rewrite Management>Rewrite Header Rules menu and look for the Rewrite Header rule 2faActivation
Once Entered in Parameter Writing Look for the Variables named ACTIVATION_CODE and in Value
we give an “ACTIVATIONCODE” at will.
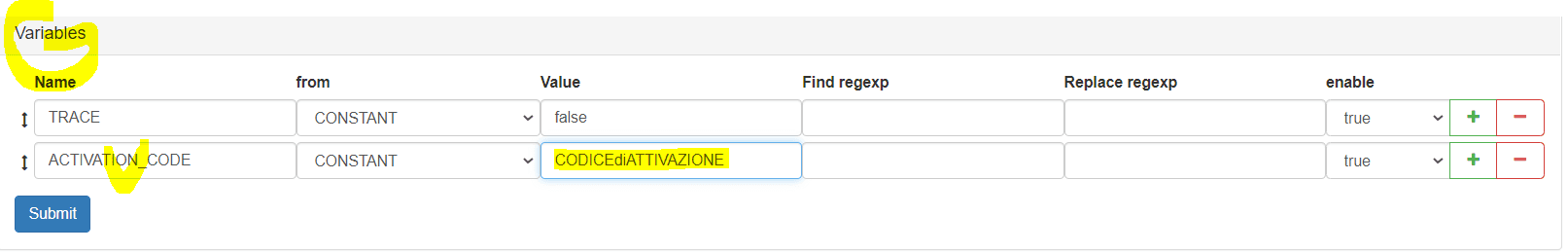
A video of the operation of insertion of ACTIVATION_CODE in the Rewrite Header Rule 2faActivation
Configuration Rewrite Header Rule 2faGeneric
We go in the Rewrite Management>Rewrite Header Rules menu and look for the Rewrite header Rule 2faGeneric
Once we got into Writing of Parameters we look for the Variables section
and insert the appropriate values to the CLIENT_KEYSTORE_NAME —> (in our example “THECertificate.p12”)
and CLIENT_KEYSTORE_PASSWORD items —> (the password received with it)

A video of the operation of Parameters insertion in the Rewrite Header 2faGeneric Rule
Application of MFA Rules
At this point it is a matter of deciding where to apply them, remembering that rewrites can be applied to Level of
ADCsGroupingsDomainsEndpoints
For this demonstration, we decided to apply them at the level of Domains, remembering however that the way of activation remains nearly the same for other entity types.
Ex. How to secure a Domain
At this point we can protect any of the resources exposed by OPLON SECURE ACCESS with a system of Multiple Factor Authentication
at this point we proceed to the implementation on a domain of MFA protection rules
we decide to protect the domain a_domain.oplon.net
Research of the Domain
ADC Settings / Domains and we look for the domain a_domain.oplon.net and get into edit
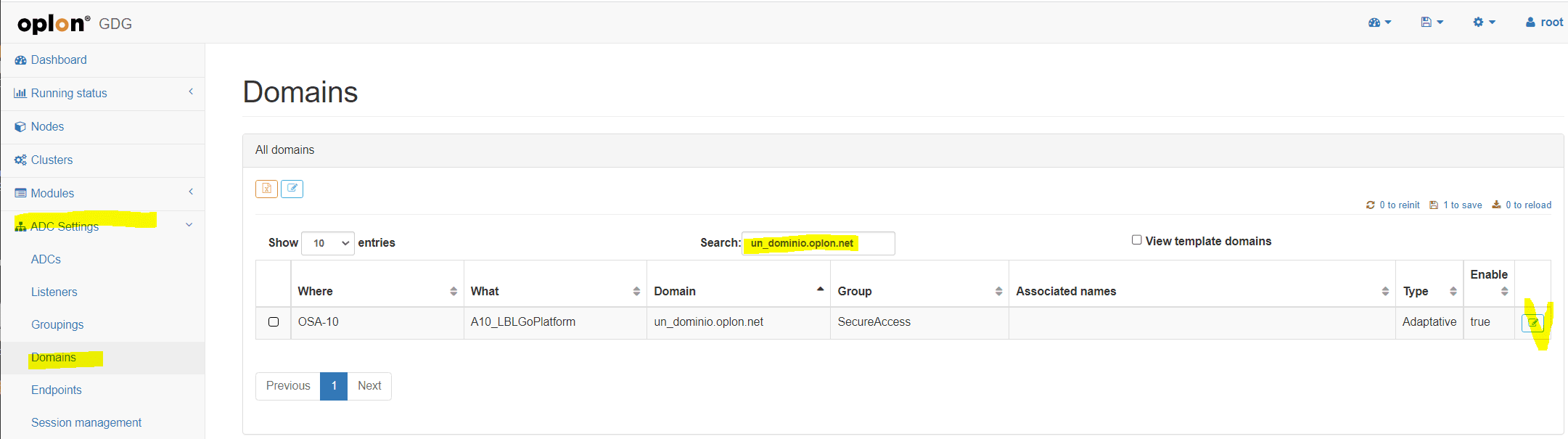
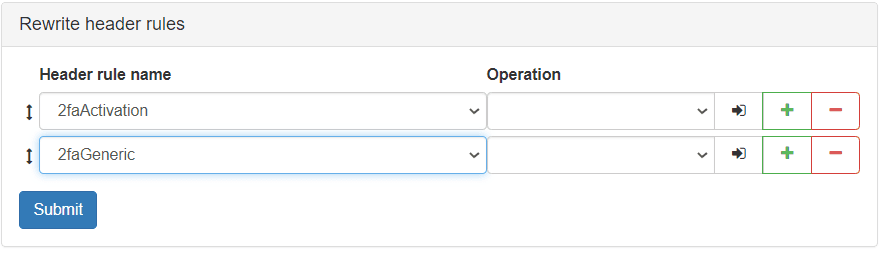
Insertion Rewrite header rules
inside the customization of the domain we look for the Rewrite header rules section
and insert the two rewrites that we did a little while ago
2faGeneric and 2faActivation.
Also remember to set 2fa Activation to the LAST value in the Operation column
Insertion Video Rewrite Rules MFA on Resource (e.g. Domain)
A video of the domain search operation and on inserting the 2faGeneric and 2faActivation rewrite header Rules