ACME SSL certificates
ACME Protocol
The ACME protocol (Automatic Certificate Management Environment) is a protocol to automate interactions between Certification Authorities and user web servers, allowing the generation and deployment of digital certificates in a simple and cost-effective way.
The ACME protocol is a protocol maintained by IETF and promoted by the Internet Security Research Group that provides a free Certification Authority service for generating digital certificates of the Domain Validation type.
This service called Let’s Encrypt is generally associated with the ACME protocol.
The ACME protocol provides several mechanisms for issuing a digital certificate for dv domain validation. The mechanism usually used is called the http challenge, in which:
-
Created a private key generates a CSR, certificate signing request containing a valid domain name.
-
The CSR is shipped to the CA Let’s Encrypt service.
-
The CA asks you to publish a key to the domain specified by the CSR. This key must be reachable by a url always indicated by the service.
-
After publishing, the CA service verifies the existence of the key.
-
If successful, the CA sends the certificate that can be published.

Figure 1 HTTP Challenge, https://letsencrypt.org/how-it-works source
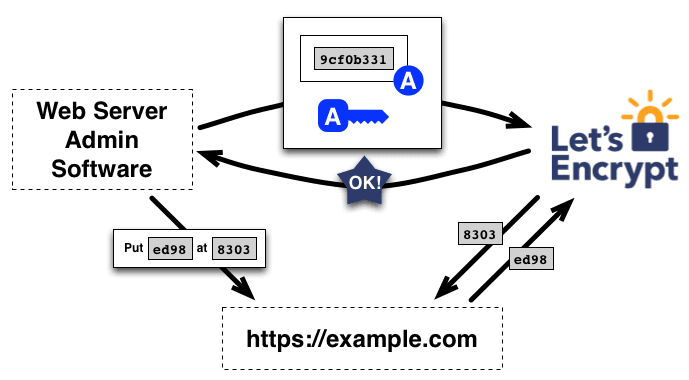
Figure 2 HTTP Challenge, source https://letsencrypt.org/how-it-works
Oplon Global Distributed Gateway and ACME
Oplon Global Distributed Gateway as the SSL Terminator ADC and SSL Offloading ADC is ideally placed for applying the ACME protocol and HTTP Challenge.
To take advantage of this feature, you must enable a rewrite rule.
The rewrite rule must be inserted in a group/virtual domain/endpoint connected to a listener on port 80
The rule intercepts CA verification requests and responds with the correct domain key to be validated.
Oplon CSR ACME Setup
In order to take advantage of the digital certificate generation feature through the ACME protocol, you must enable the rewrite rule LBLHttpAcmeChallengeCsr ADC form through which the domain to be validated is provided.
Through the ADC Settings menu, select Rewrite management and then Rewrite header rules.
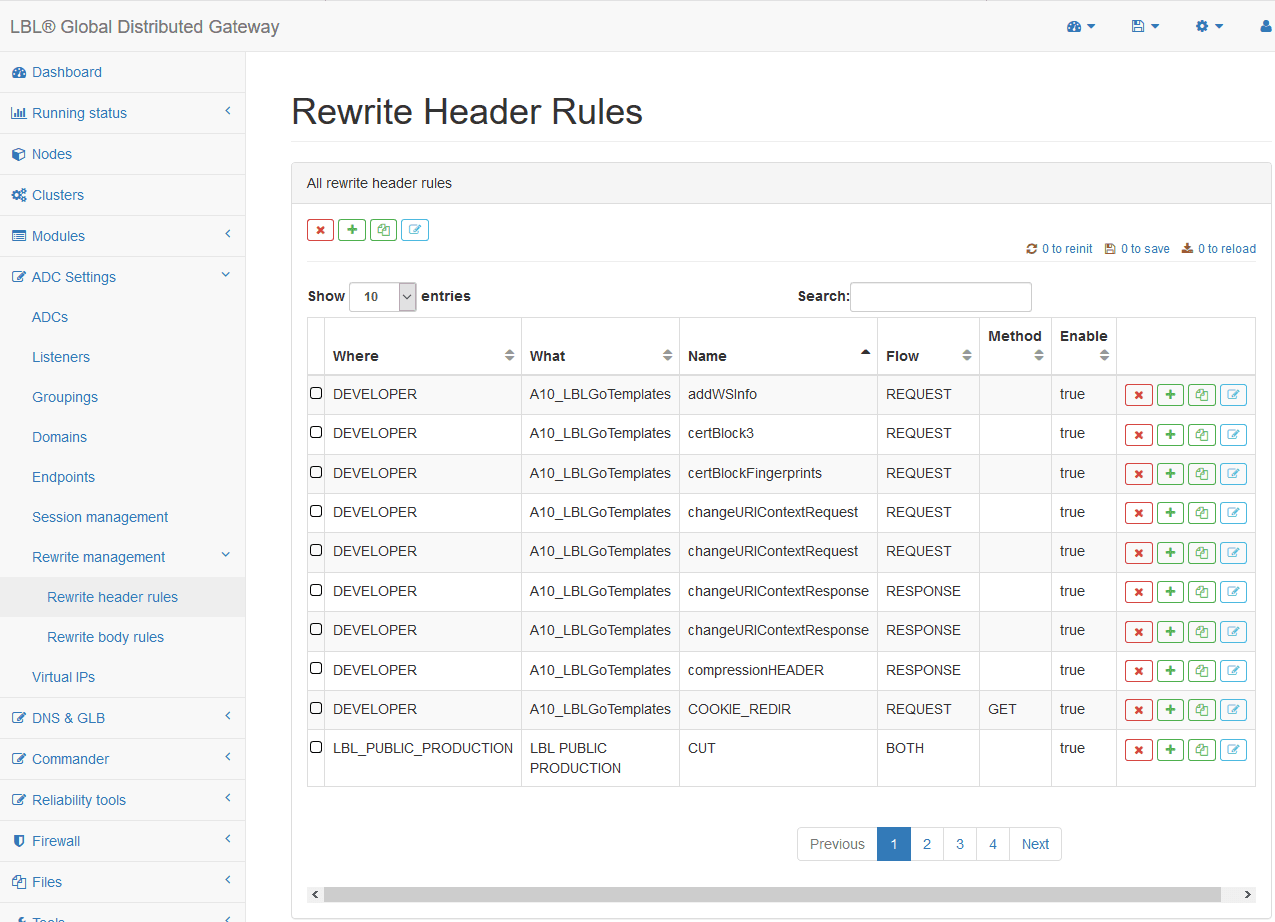
Figure 4 ADC Settings > Rewrite management > Rewrite header rules
Through the search field, search for the LBLHttpAcmeChallengeCsr rule.
Simply use “acme” as a filter.
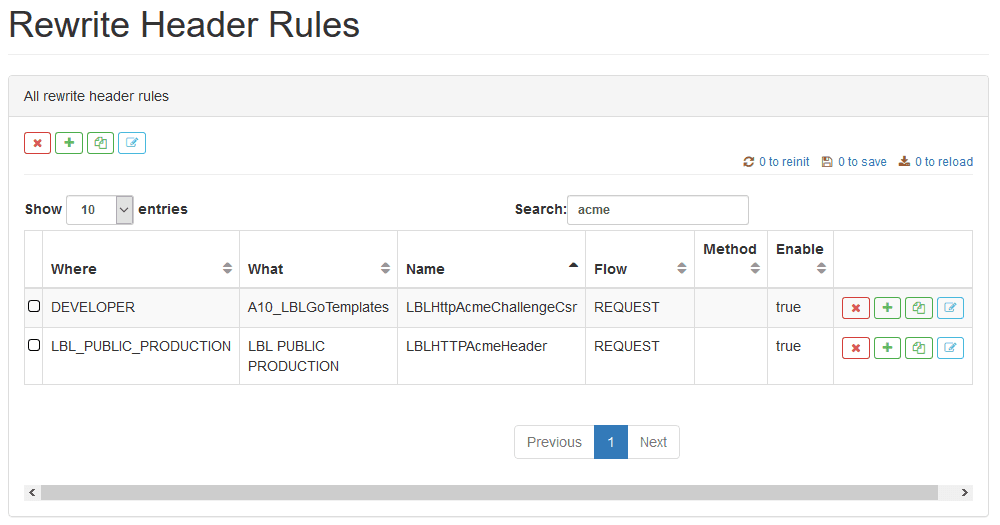
Figure 5 LBLHttpAcmeChallengeCsr search, using acme as a filter.
Select the rule LBLHttpAcmeChallengeCsr template module and copy it to the balancing module that provides the domain services to be validated.
You must now apply the rule to the balancing module.
Through the ADC Settings menu, select ADCs.
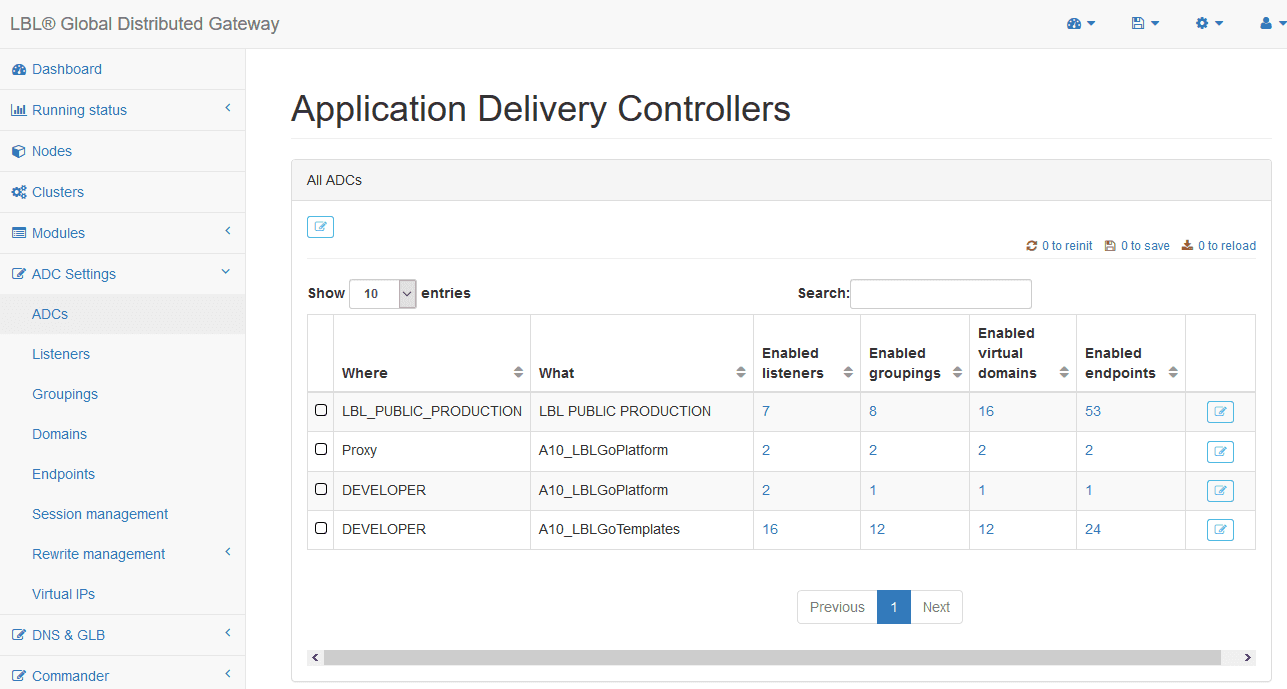
Figure 6 ADC Settings > ADCs
Enter the ADC module configuration mask
Open the Default rewrite rules panel, in the parameter rewriteHeaderRules property LBLHttpAcmeChallengeCsr.
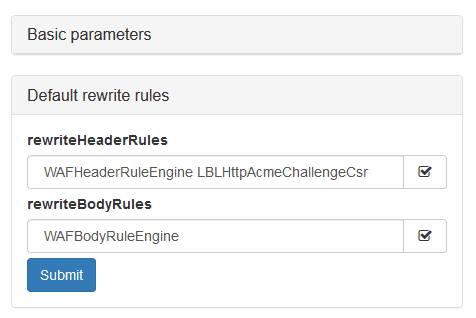
Figure 7 Inserting the LBLHttpAcmeChallengeCsr rule in the default rewrite rules of an ADC
Save your changes and reinitialize the ADC module using the links in the upper right.
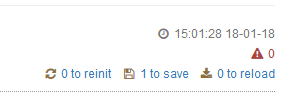
Figure 8 Save and Reinitialization Reporting Links
SSL Certificate Generation
Through the menu, select Files and then Keystore.
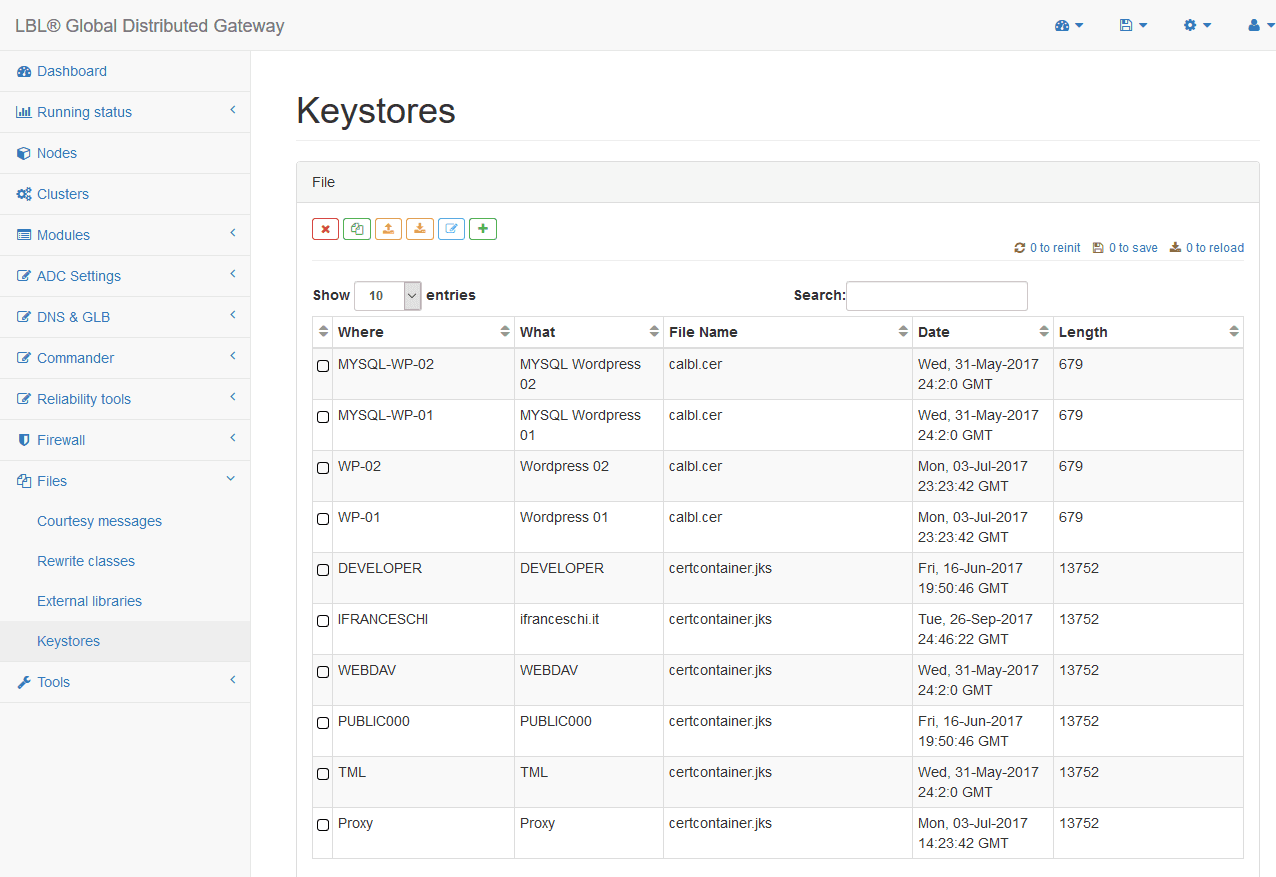
Figure 9 Menu Files > Keystores to get the list of keystores present
The view lists all keystores, containers of digital certificates.
Select the correct keystore and press the edit button.
For editing, you must enter the password of the keystore.
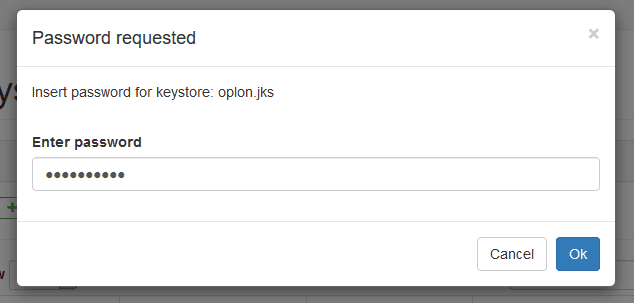
Figure 10 Entering password for keystore.
To generate a new certificate, press the new key
![]()
For domain validation, simply enter the domain name in the cn (common name) field.
Enter the same password in the alias field that you typed for the keystore.
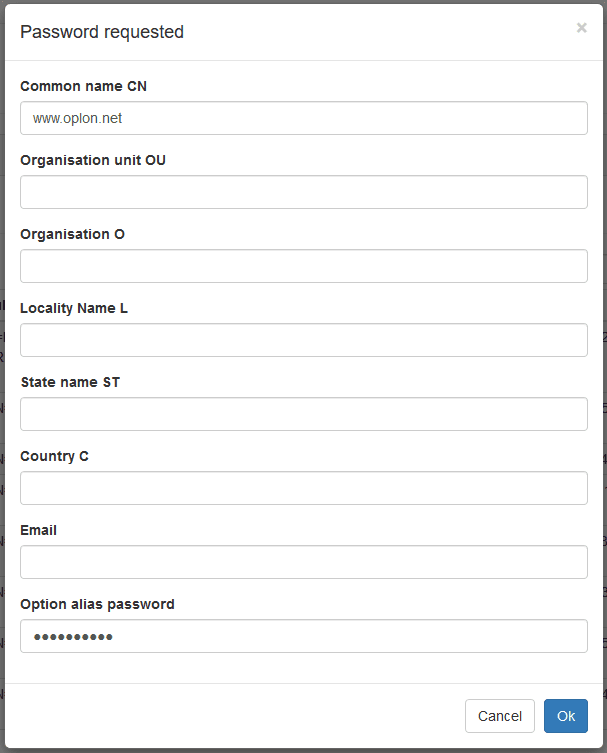
Figure 11 Creating a new certificate. CN and Password Alias are required
The new certificate is entered in the keystore.
The name of the certificate issuer is the same as the name of the domain that you entered. The certificate is not yet signed by the CA.
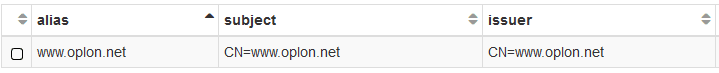
Figure 12 Subject and Issuer match in certificates not signed by the CA.
To generate and send the CSR, simply select the certificate you created and press the CSR build button
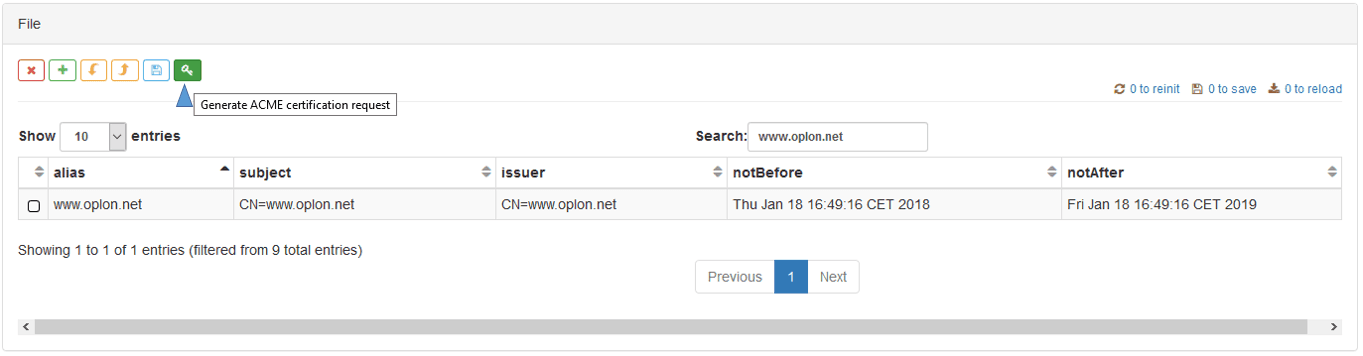
Figure 13 Generating and sending CSR to Let’s Encrypt for certificate signing
You must enter the password alias for submission.
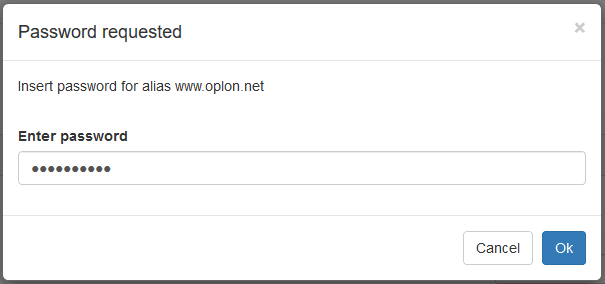
Figure 14 Entering Password Alias
The certificate is signed.
Figure 15 CSR successfully occurred.
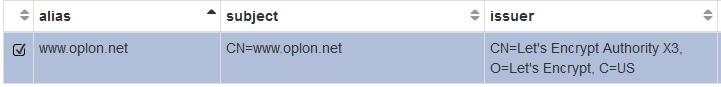
Figure 16 The issuer name matches the name of the CA
Save the keystore through the save button to confirm your changes.